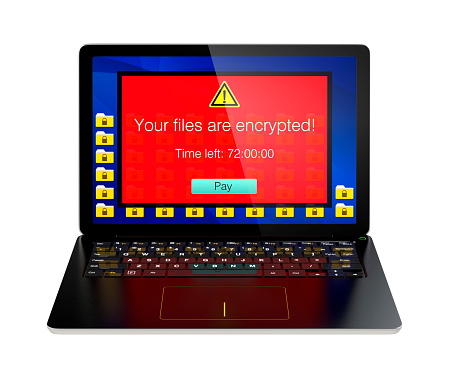
Humanity is rapidly hurtling forward at a breakneck speed toward a high-tech reality dominated by web-enabled mobile devices. The average worker’s typical workday has been revolutionized over the past couple of decades. For all the good that these improvements in technology have brought, there is still a downside that cannot be denied: Data security vulnerabilities. Mobile devices are highly susceptible to malware, hacks and other malicious attacks that often render hardware and software inoperable.
Flexible Office Environments Aren’t Properly Prepared to Fend Off Digital Attacks
The number of United States-based mobile employees will top the 105 million mark by 2020. We are collectively moving toward a new way of working in which employees telecommute from home, libraries or other off-site spaces. This improved mobility saves time and improves flexibility, but increased mobility also represents a legitimate digital security threat.
The unfortunate truth is that businesses are not properly prepared to combat hacks, malware and other digital attacks targeted at web-enabled mobile devices. In a recent study by Shred-It, their Security Tracker Information Security Survey showed that United States business leaders have not put the necessary protocols in place to safeguard data stored on the cloud or web-enabled electronic devices like smartphones, USBs, tablets and laptops. Furthermore, the survey revealed that the vast majority of business leaders have failed to provide employees with adequate training to prevent digital breaches.
A Look at the Numbers
According to Shred-it’s survey, a whopping 92 percent of C-Suite Executives and nearly 60 percent of small business owners employ at least a couple employees who work from home or off-site. The problem is that just under one-third of those surveyed have implemented an information security policy for their flexible working spaces and off-premises work environments. In today’s age of web ubiquity, these percentages are frighteningly low.
These businesses are facing unnecessary risks that could be easily mitigated with the adoption of comprehensive security protocols. Some of the largest corporations have implemented such protocols as a part of their comprehensive security efforts, but small to medium-sized businesses have plenty of work to do when it comes to safeguarding the storage, transmission and destruction of digital data.
Nearly 40 percent of small business owners reported that they wipe electronic devices without the assistance of outside digital security aficionados. This is an unwise move because it puts private data at risk when the devices are eventually refurbished or recycled. Plenty of small to medium-sized businesses have legacy hardware stacked in back offices and other storage spaces. This might not seem like a critical security mistake to a layman, but any business owner who has suffered a break-in will explain the importance of moving everything with a hard drive off-site for a thorough wipe conducted by digital security professionals.
A Proactive Defense
A wipe is only half the battle against data breaches. The other half is a physical destruction of the hard drive to ensure that all important data is totally removed. It is time for business owners and managers to re-think their security policies with today’s unique threats in mind. Protocols should also be put in place for the destruction of confidential documents. Too many off-site employees trash such paperwork in a haphazard manner, assuming they won’t be targeted by a criminal just because they work away from the office. All phones and hard drives should be encrypted and password-protected. Perhaps most important is the ongoing training of employees in an effort to keep them abreast of the latest threats.
Centerpoint IT
Centerpoint IT is the trusted choice when it comes to staying ahead of the latest information technology tips, tricks, and news. Contact us at (404) 781-0200 or send us an email at info@centerpointit.com for more information.
Call our business managed IT services department directly at (404) 777-0147 or simply fill out this form and we will get in touch with you to set up a getting-to-know-you introductory phone call.
Fill in our quick form
We'll schedule an introductory phone call
We'll take the time to listen and plan the next steps
11285 Elkins Rd Suite E1, Roswell, GA 30076
© Copyright 2024 Centerpoint IT. All Rights Reserved. Website in partnership with Tech Pro Marketing. | Privacy Policy
Get Immediate Help For All Your Technology Issues (404) 777-0147

If you want our team at Centerpoint IT to help you with all or any part of your business IT, cybersecurity, or telephone services, just book a call.
Fill in your information below to get started today.
"*" indicates required fields
Fill in your information below to schedule now.
"*" indicates required fields
Before your organization commits to 1, 2, 3 or even longer managed IT services contract, understand what you’re getting. Centerpoint IT gives you the facts in our Managed IT Services Buyer’s Guide.
Enter your information below and we’ll send it over.
"*" indicates required fields

We are turning 15 and want to celebrate this milestone with you because without you this would not have been possible. Throughout this year look for special promotions on services and tools aimed at Making IT Simple for You so you can focus on your business.

We are turning 15 and want to celebrate this milestone with you because without you this would not have been possible. Throughout this year look for special promotions on services and tools aimed at Making IT Simple for You so you can focus on your business.
https://calendly.com/centerpoint-it/discovery-call